On July 11th, Microsoft announced that Azure AD would be renamed to Microsoft Entra ID. Microsoft also announced two new security offerings called Microsoft Entra Internet Access and Microsoft Entra Private Access as part of a Security Service Edge (SSE) solution. SSE covers the security aspects of a Secure Access Service Edge (SASE) solution.
In this article I’m digging into what these two new offerings bring to the table, and more importantly what problems they solve. I’ll start with explaining what Security Service Edge (SSE) and Secure Access Service Edge is, what problems they solve and how Microsoft will implement these solutions.
What is Secure Access Service Edge (SASE) and Security Service Edge (SSE)?
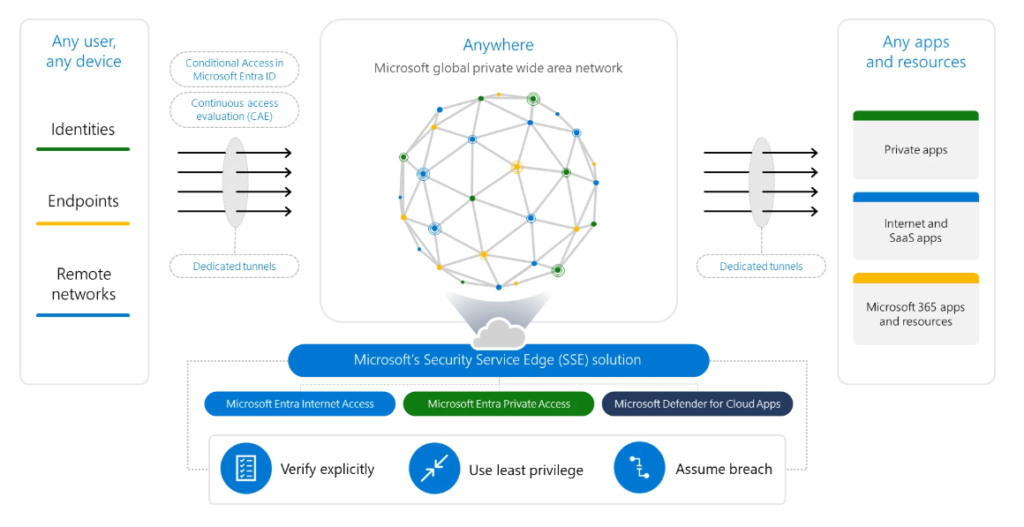
SASE was defined in 2019, by market analyst Neil MacDonald and Joe Skorupa from Gartner. SASE merges Software Defined Wide Area Networks (SD-WAN) with security functions. It provides users with secure access to resources regardless of location, for both cloud and on-premises environments. It also provides continuous authentication and authorization.
The security functions provided are Cloud Access Security Brokers (CASB), Secure Web Gateways (SWG), AV/Malware inspection, Virtual Private Network (VPN), Firewalling as a Service (FWaaS) and Data Loss Prevention (DLP) and are part of the Security Service Edge (SSE) solution.
What problem does a SASE and SSE solution solve?
Where traditionally we would provide access to on-premises resources from anywhere using Virtual Private Network (VPN) solutions, we access public accessible services using the internet connection we have at our disposal. Some companies choose to fully tunnel their VPN clients so that both on-premises resources and public resources are accessed via the corporate network, while many other VPN solutions use the concept of split-tunneling to provide access to both on-premises network (via the VPN) and public resources (via internet)
Using VPN solutions has some disadvantaged though, for example your VPN clients connect to a VPN concentrator which is usually available in one location, also VPN solutions offer LAN extension meaning that clients connected to the VPN solution are becoming part of the LAN network which gives some challenges from a security perspective.
In this traditional way of providing access to on-premises resources, all it takes is one compromised user account, infected device or open port and an attacker can gain access to and move laterally anywhere inside the network.
SASE is capable of providing secure access to resources no matter where they are located or how they are accessed. Which basically means that clients connect through local points of presence (PoPs) to the SD-WAN, within that WAN security services make sure that the clients are protected, and from that WAN they are also able to connect to on-premises resources in a secure way because every connection is authenticated and needs to be authorized.
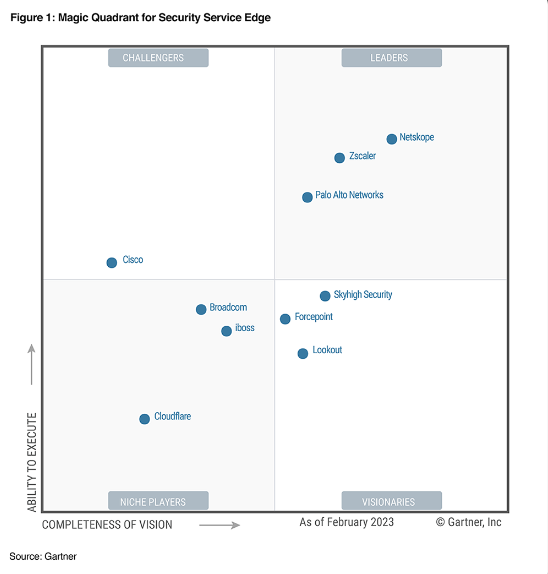
Who is providing Security Service Edge solutions already?
As you can see in the latest Gartner Magic Quadrant for Security Service Edge below, you can see that currently company’s like Netskope, Zscaler and Palo Alto Network are already providing SSE solutions.
If you want to know more about the Gartner Magic Quadrant for Security Service Edge products I advise you to download the 2023 report provided by one of the companies mentioned above. Here is the link to the report provided by Netskope: https://www.netskope.com/lp-2023-magic-quadrant-for-security-service-edge-sem – keep in mind that you need to leave your contact details in order to be able to download the report.
Why is Microsoft stepping into the SASE and SSE solution market?
With more and more companies moving to leveraging cloud technology, keeping attackers away from company assets is not a matter of implementing a firewall anymore. Today we need to protect identities of users, since the identity of users provides access to company data stored in SaaS based applications.
Microsoft is seeing an increase in cyberattacks with the goal to get access to corporate identities. In the last 12 months, Microsoft saw an average of more than 4,000 password attacks per second, an almost threefold increase from the 1,287 attacks per second Microsoft saw the previous year. And that is a lot.
Many companies have tried to mitigate the risk of password attacks by implementing Multi Factor Authentication (MFA) for their users, and even though MFA provides an extra layer of security, attackers are already finding ways to phish users by using Adversary-in-the-Middle (AiTM) attacks, also known as man-in-the-middle (MitM) attacks. Even though circumventing these AiTM attacks using techniques like passkeys can be mitigated, the whole phishing corporate users issue is a cat and mouse game where attackers continue to find ways to trick users into providing their credentials to bad actors.
In order to address the challenges mentioned above, Microsoft is adding an identity-centric network access solution to their arsenal. By converging controls for identity and network access you can create provide protection and governance using Conditional Access policies.
How is Microsoft stepping into the SASE and SSE solution market?
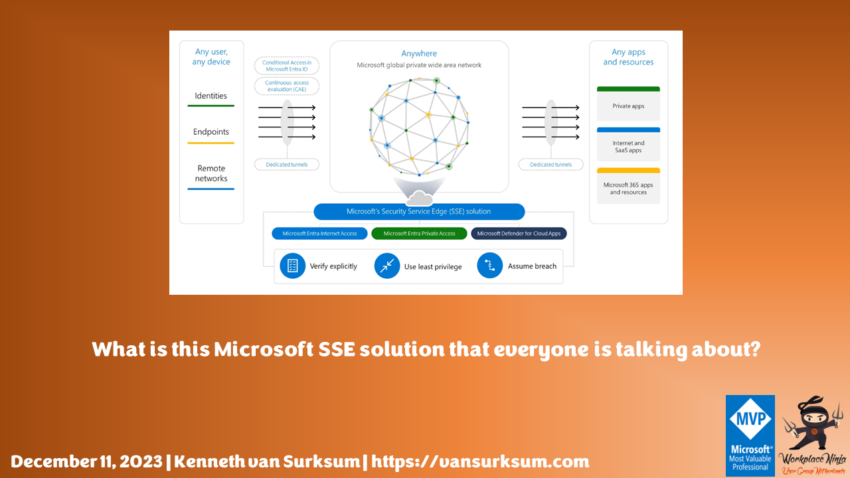
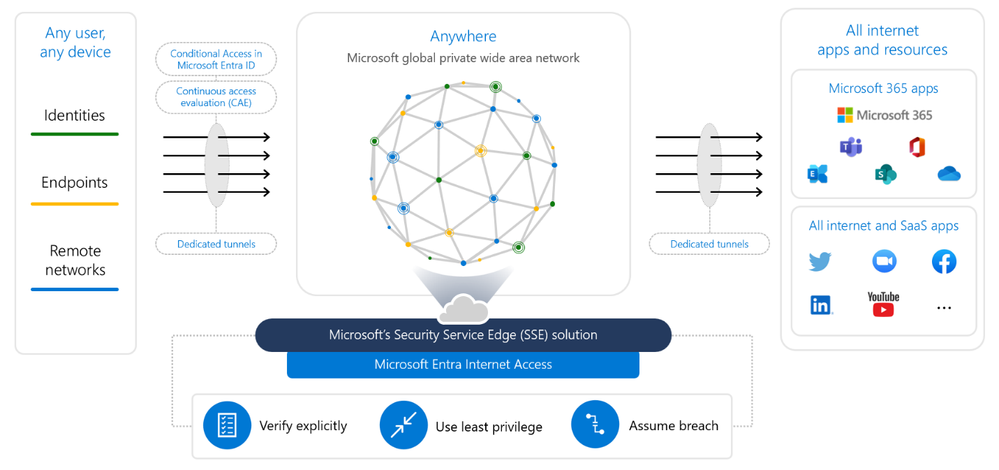
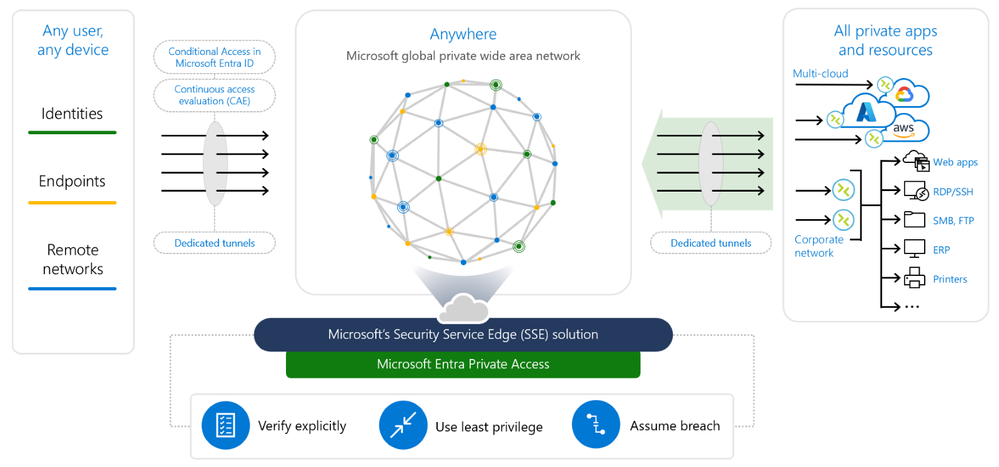
Microsoft has announced two new products called “Microsoft Entra Internet Access” and “Microsoft Entra Private Access” which are part of what Microsoft calls Global Secure Access (GSA). GSA, together with Microsoft Defender for Cloud Apps (MDA/MDCA), which is Microsoft’s CASB solution provides the Microsoft SSE offering.
Microsoft Entra Internet Access (Public Preview)
Microsoft Entra Internet Access is a Secure Web Gateway (SWG) solution leveraging the Microsoft SD-WAN. A SWG is capable of blocking access to or from malicious websites and links and can enforce company policies. It includes URL filtering, malicious code detection and filtering and provides application controls for web based applications. Looking at already existing solutions from Microsoft the SWG has similar functionality as Network Filtering capabilities provided by Microsoft Defender for Endpoint, and the application controls for web based applications provided by Microsoft Defender for Cloud Apps.
By leveraging Microsoft Entra Internet Access in combination with Microsoft Entra Conditional Access we can for example define that access to Microsoft 365 services can only be made when coming from the Microsoft Entra Internet Access. Users must be connected to that environment first before being able to access their Email hosted on Exchange Online, or access documents stored in SharePoint online. And while on Microsoft Entra Internet Access, we can protect the access to the rest of the internet in order to circumvent malicious internet traffic.
So to go back to the traditional VPN solution, Microsoft Entra Internet Access can be a replacement for the scenario’s where devices now use full tunnel solutions in order to be able to access the internet.
Global Secure Access Client
Clients connect to Microsoft Entra Internet Access using a Global Secure Access (GSA) client or by being present on a network location which is connected to the Microsoft SD-WAN. The GSA client is currently provided for Windows (in Preview) but it seems logical that GSA clients will be made available for other platforms as well. See the following article for more information about how to install the GSA client for Windows: The Global Secure Access Client for Windows (preview) – Global Secure Access | Microsoft Learn. Microsoft has also announced clients for Android in public preview, and for MacOS and iOS in private preview.
Microsoft Entra Private Access (Public Preview)
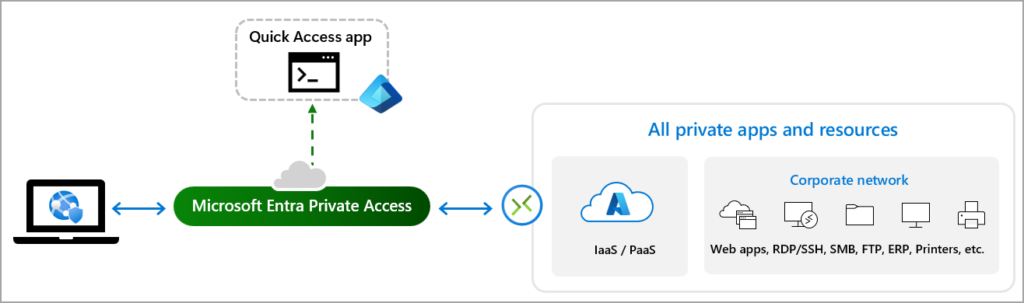
Once devices are connected to the Microsoft Entra Internet Access service, we can provide access to on-premises resources by using the Microsoft Entra App Proxy functionality. For this the App Proxy that we know today which is capable of reverse proxy-ing HTTP/HTTPS traffic will be upgraded to support reverse proxy-ing any TCP/UDP traffic.
Read more on how to configure App Proxy connectors for Microsoft Entra Private Access.
With this upgrade we can also make resources like Fileshares, Printers, Remote Desktop Protocol (RDP) connections but also custom applications where locally installed clients access backend resources over custom ports available to clients from the internet.
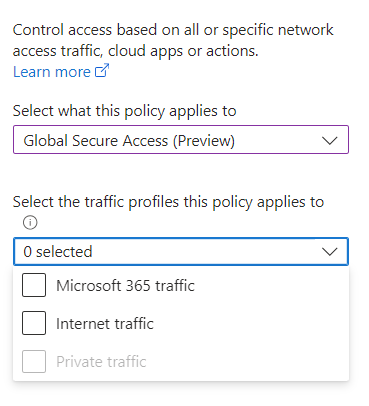
How can we use it with Conditional Access?
Within Conditional Access, a new target is added called Global Secure Access. When selecting Global Secure Access as a target within your Conditional Access policies you can select so called traffic profiles. Currently the following traffic profiles can be selected:
- Microsoft 365 traffic
- The Microsoft 365 traffic forwarding profile includes SharePoint Online, Exchange Online, and Microsoft 365 apps.
- Internet traffic
- The traffic going to the internet
- Private traffic
- The traffic going to the App Proxy
Traffic profiles as they are called within Conditional Access are actually traffic forwarding profiles. The traffic forwarding profile allows you to configure the type of network traffic to tunnel through the Global Secure Access solution. You need to configure Quick Access which is the configuration needed in order to forward traffic to on-premises resources through the App Proxy. Quick Access will create an Enterprise Application which you can target in your Conditional Access policy as a target application.
So, what kind of scenario’s can we build now?
- Block access to internet for High-Risk users
- Only allow access to on-premises resources from compliant devices
- Accept terms of use before allowing access to Internet
Conclusion
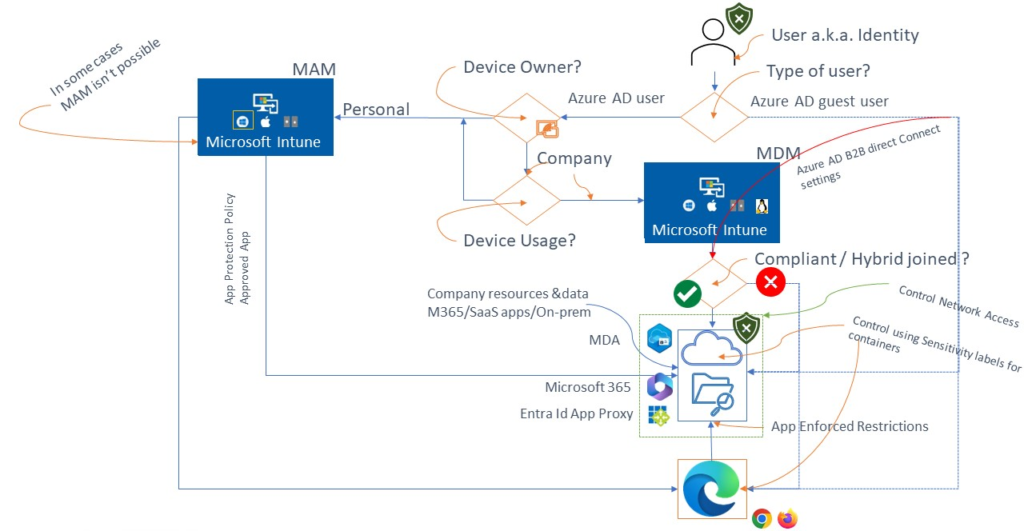
A lot of new terminology to digest for this new addition which adds networking into the game of Identity and data protection that we normally cover by implementing Conditional Access. For people familiar with my Conditional Access policy framework, this will lead to the following diagram. In the diagram the “Control Network Access” and Entra ID App Proxy functionality has been added.
Global Secure Access has the following licensing requirements: The preview requires a Microsoft Entra ID P1 license. If needed, you can purchase licenses or get trial licenses. To use the Microsoft 365 traffic forwarding profile, a Microsoft 365 E3 license is recommended. After general availability, Microsoft Entra Private Access and Microsoft Entra Internet Access might require different licenses.
As far as I know Microsoft hasn’t officially announced pricing yet, or if any additional licensing is needed.
Want to know more about Conditional Access, download my paper on the subject providing lots more context on the subject below
1 thought on “What is this Microsoft SSE solution that everyone is talking about?”