One of the scenario’s we can build with Conditional Access, is the scenario where we restrict access inside the web application itself. By doing so, you could for example limit the functionality of the web applications on non-managed devices, or when accessing the web application from a country where your company normally doesn’t operate. The web applications can be configured to behave differently if the user is applicable for a Conditional Access policy where App Enforced restrictions are configured.
Within the Office 365 suite of applications, the following web applications are supported for App Enforced Restrictions:
- Outlook Web Access
- SharePoint and OneDrive
In this post I will go into detail on how to setup these app enforced restriction and what the expected behavior will be from an end-user perspective.
Update December 2020: I’ve written another article on this subject which might be interesting as well: Defining more granularity for your Conditional Access App Enforced Restrictions using Sensitivity Labels
Configure Outlook Web Access for limited access via App Enforced Restrictions
Before you can enable Conditional Access App Enforced Restrictions you first need to enable the feature in the default OWA mailbox policy, since by default this functionality is turned off, this can be done using the Set-OwaMailBoxPolicy cmdlet as part of the Exchange Online PowerShell module.
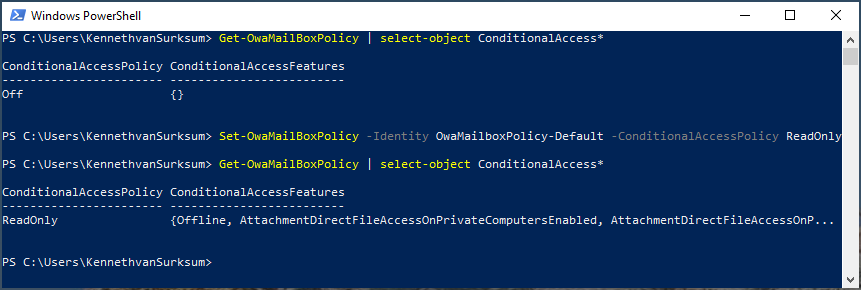
First request the current status of the OWA mailbox policy by executing the following command: Get-OwaMailBoxPolicy |select-object ConditionalAccess*. This command will return the current status of the ConditionalAccessPolicy (On or Off) and the ConditionalAccessFeatures.
If the ConditionalAccessPolicy is set to Off, you can enable the functionality which allows for restrictions when used in combination with a Conditional Access App Enforced Restriction policy. You have either the option to configure the policy in two modes:
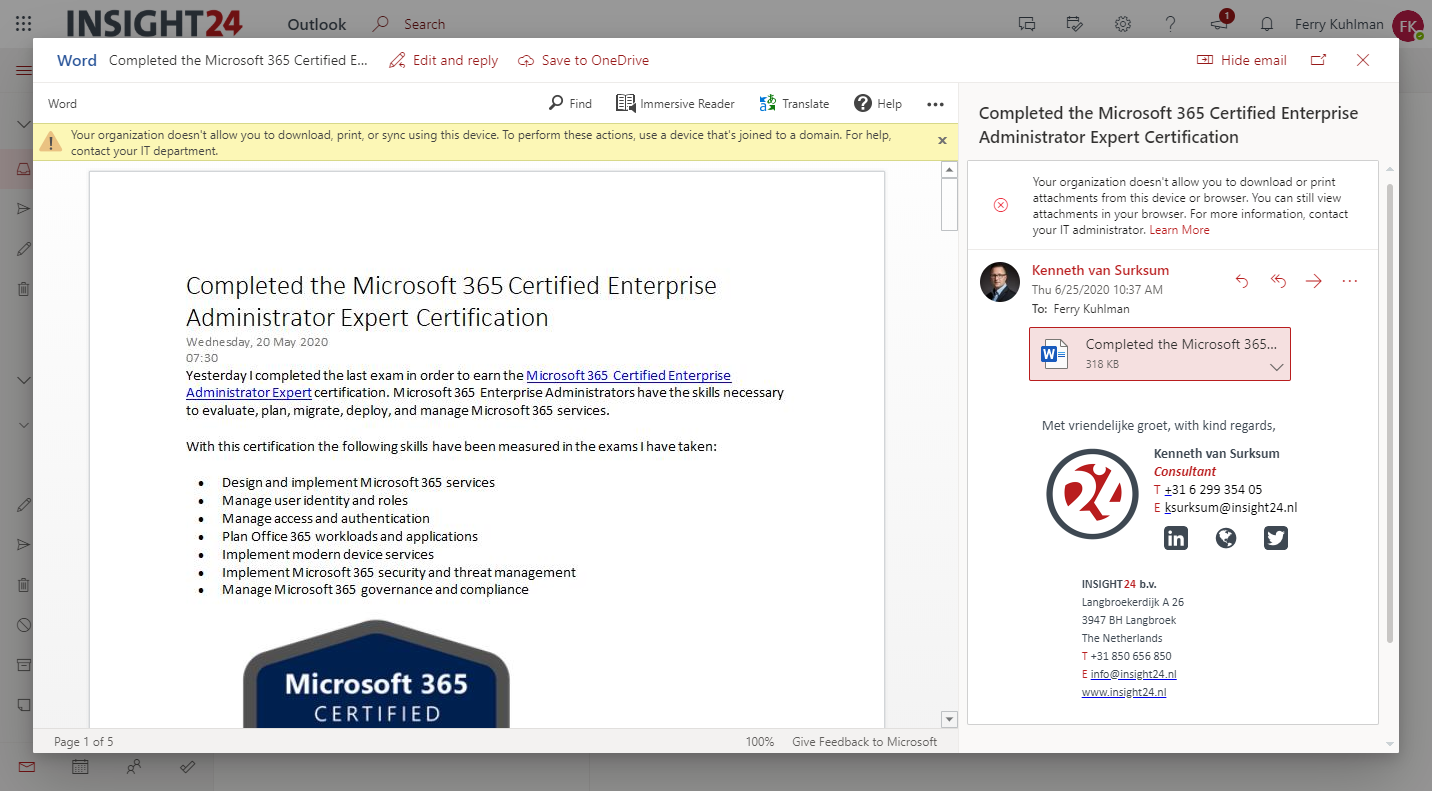
- ReadOnly, where users can’t download attachments to their local computer, and can’t enable Offline Mode on non-compliant computers
- ReadOnlyPlusAttachmentsBlocked, in the ReadOnly setting viewing attachments in the browser is possible, when using this setting viewing attachments in the browser is blocked.
In this example we are going to enable the ConditionalAccessPolicy in the OWA Mailbox Policy and use the ReadOnly mode, this can be accomplished by executing the following command: Set-OwaMailBoxPolicy -Identity OwaMailboxPolicy-Default -ConditionalAccessPolicy ReadOnly
After executing the command make sure that you check whether the setting was succesfull by executing the Get-OwaMailBoxPolicy |select-object ConditionalAccess* command again and check whether the ConditionalAccessPolicy is set to ReadOnly
Configure SharePoint Online and OneDrive for limited access via App Enforced Restrictions
SharePoint Online and OneDrive can be configured in several ways. The first option is to set a Global setting which becomes effective for all SharePoint Online and OneDrive sites in your environment, and the Per site option allows you to specify options per site.
Global settings
The Global or organizational-wide settings can be configured from the SharePoint admin center (https://<tenantname>-admin.sharepoint.com). In the SharePoint Admin center select Policies | Access Control and select Unmanaged devices.
By default, for unmanaged devices the option “Allow full access from desktop apps, mobile apps, and the web” is selected, and by modifying the option to either “Allow limited, web-only access” or “Block access” you configure limited access for your whole environment.
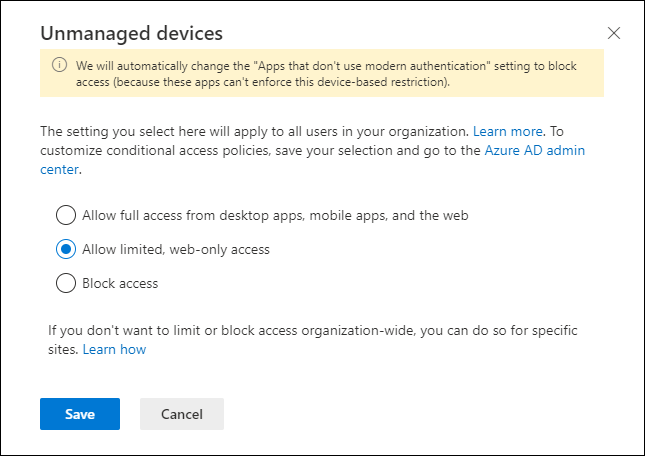
If you configure the unmanaged devices settings, 2 new Conditional Access policies will be created. While I’m not a big fan of letting a setting like create the Conditional Access policies for you, they do provide some valuable information. I would therefore suggest to let the wizard create them, and that you turn them off immediately after creation. Keep in mind that if you are playing with these, it might be that several Conditional Access policies are created (one per day, since the day when created in defined in the name).
Also note that if you use the PowerShell way to create the setting in the SPOtenant, the policies will also be created and are active for all your users. (which can have impact if you want to test first).

The first one “[SharePoint admin center]Block access from apps on unmanaged devices – 2020-06-25” has the following properties
| Name | [SharePoint admin center]Block access from apps on unmanaged devices – 2020-06-25 | ||
| Assignments | |||
| Users and Groups | All Users | ||
| Cloud apps or actions | Office 365 SharePoint Online | ||
| Conditions | |||
| Client Apps | Modern Authentication Clients | ||
| Access controls | |||
| Grant | Require device to be marked as compliant OR Require Hybrid Azure AD joined device |
So, to summarize this policy grants access to either Compliant Azure AD joined devices or Hybrid joined (AD joined, Azure AD registered) devices when the client supports Modern Authentication while accessing SharePoint Online.
So having clients which support Modern Authentication is crucial for this, I’ve already written a lot more on this topic for which you can find the latest information here: “May 2020 update of the Conditional Access Demystified Whitepaper, Workflow cheat sheet, Implementation workflow and Documentation spreadsheet”
The second one “[SharePoint admin center]Use app-enforced Restrictions for browser access – 2020-06-25” has the following properties
| Name | Use app-enforced Restrictions for browser access – 2020-06-25 | ||
| Assignments | |||
| Users and Groups | All Users | ||
| Cloud apps or actions | Office 365 SharePoint Online | ||
| Conditions | |||
| Client Apps | Browser | ||
| Access controls | |||
| Session | Use app enforced restrictions |
This conditional access policy when applicable gives SharePoint online, the signal that the limited access is applicable.
Per site settings
For a basic environment, having these global settings might be enough, but perhaps you want to more granularly control whether you want the limited access applied to a SharePoint or OneDrive site. This can be accomplished by using PowerShell (for now, more on that later) and described in the following section “Block or limit access to a specific SharePoint site or OneDrive” of the article: “Control access from unmanaged devices” in the SharePoint online documentation.
In order to use PowerShell you must have the SharePoint Online Management Shell installed, once installed, you can connect using
Connect-SPOService -Url https://<tenantname>-admin.sharepoint.com which will log you in, into the Management Shell
From there you can determine the current status of a particular SharePoint site using the following command.
Get-SPOSite -Identity https://<SharePoint online URL>/sites/<name of site or OneDrive account> -Detailed | fl Conditional*
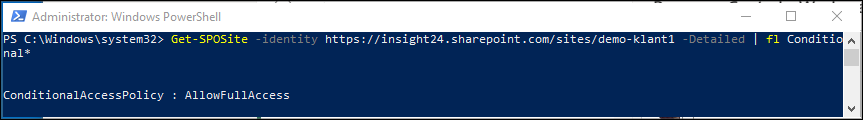
As you can see, this command has a strange outcome, since on a Global level we just defined Read Only Access. Turns out that if you specify the setting on site level, this will override the global policy. So for example, you could set the option “Allow limited, web-only access” as described above in the Global policy, but define a setting to Block Access on the Site level.
You can set the policy on a site level by executing the following command: Set-SPOSite -Identity https://<SharePoint online URL>/sites/<name of site or OneDrive account> -ConditionalAccessPolicy <value>
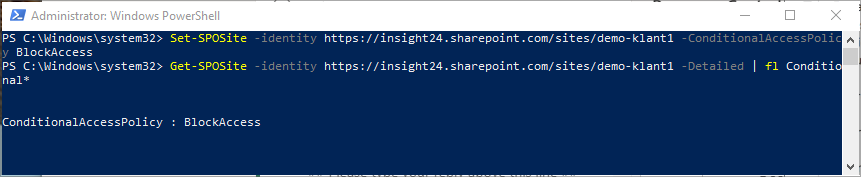
For the ConditionalAccessPolicy parameter the following values are available:
- AllowFullAccess: The default setting
- AllowLimitedAccess: The setting allowing limited access
- BlockAccess: Blocks access
When using the AllowLimitedAccess option, you can supply additional parameters to further define the behavior, as detailed in “Advanced Configurations“, for example you can provide the option -LimitedAccessFileType OtherFiles after the -ConditionalAccess AllowLimitedAccess parameter to allow users to download files that can’t be previewed, such as .ZIP files.
If you have to specify this for a lot of SharePoint sites, you can of course automate these settings, but wouldn’t it be nice if we could enable this from the GUI while creating the SharePoint site, or while the SharePoint site is created as part of a Teams environment .
Sensitivity labels for Containers
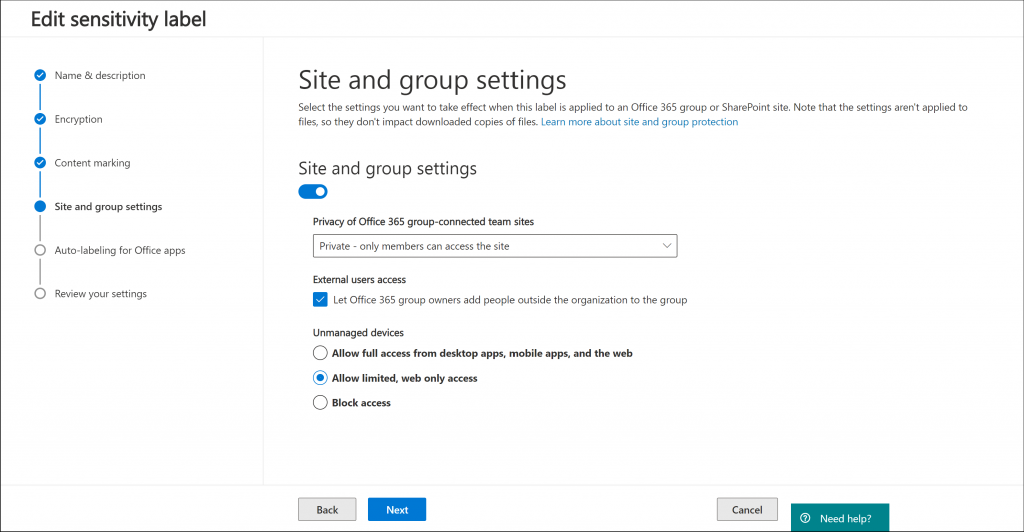
Microsoft is currently rolling out new functionality which allows you to specify the behavior described above by making use of Sensitivity Labels and apply them to so called “containers” (announcement here: General Availability: Microsoft Information Protection sensitivity labels in Teams/SharePoint sites). These containers are either Microsoft Teams, Microsoft 365 Groups and SharePoint sites. Once enabled, the Sensitivity label will receive the “Site and group setting” options as detailed in the picture below.
The idea is that when creating one of the containers, you must specify the Sensitivity as well. In the Sensitivity label you can define which setting related to the ConditionalAccessPolicy parameter on the container you want to assign. You also have the possibility to assign a sensitivity label to already existing Team or SharePoint sites.
Once this functionality is available in your tenant, you can use the sensitivity label to specify the access to the environment when App Enforced Restrictions are in use.
See: Use sensitivity labels to protect content in Microsoft Teams, Microsoft 365 groups, and SharePoint sites (public preview) and also read this very insightful article by Joanne C Klein titled: “Site Sensitivity and the documents within“
Create the Conditional Access Policy
Now that we created the necessary settings in both the OWA mailbox policy and SharePoint, we can define a Conditional Access policy or modify the automatically created Conditional Access policies for our scenario.
| Name | I24 – Block access from apps on unmanaged devices to EXO and SPO | ||
| Assignments | |||
| Users and Groups | All Users, except Break Glass accounts | ||
| Cloud apps or actions | Office 365 SharePoint Online, Office 365 Exchange Online | ||
| Conditions | Client Apps | Modern Authentication Clients | |
| Access controls | |||
| Grant | Require device to be marked as compliant OR Require Hybrid Azure AD joined device |
| Name | I24 – Block access from apps on unmanaged devices to EXO and SPO | ||
| Assignments | |||
| Users and Groups | All Users, except Break Glass accounts | ||
| Cloud apps or actions | Office 365 SharePoint Online, Office 365 Exchange Online | ||
| Conditions | |||
| Client Apps | Browser | ||
| Access controls | |||
| Session | Use App Enforced Restrictions |
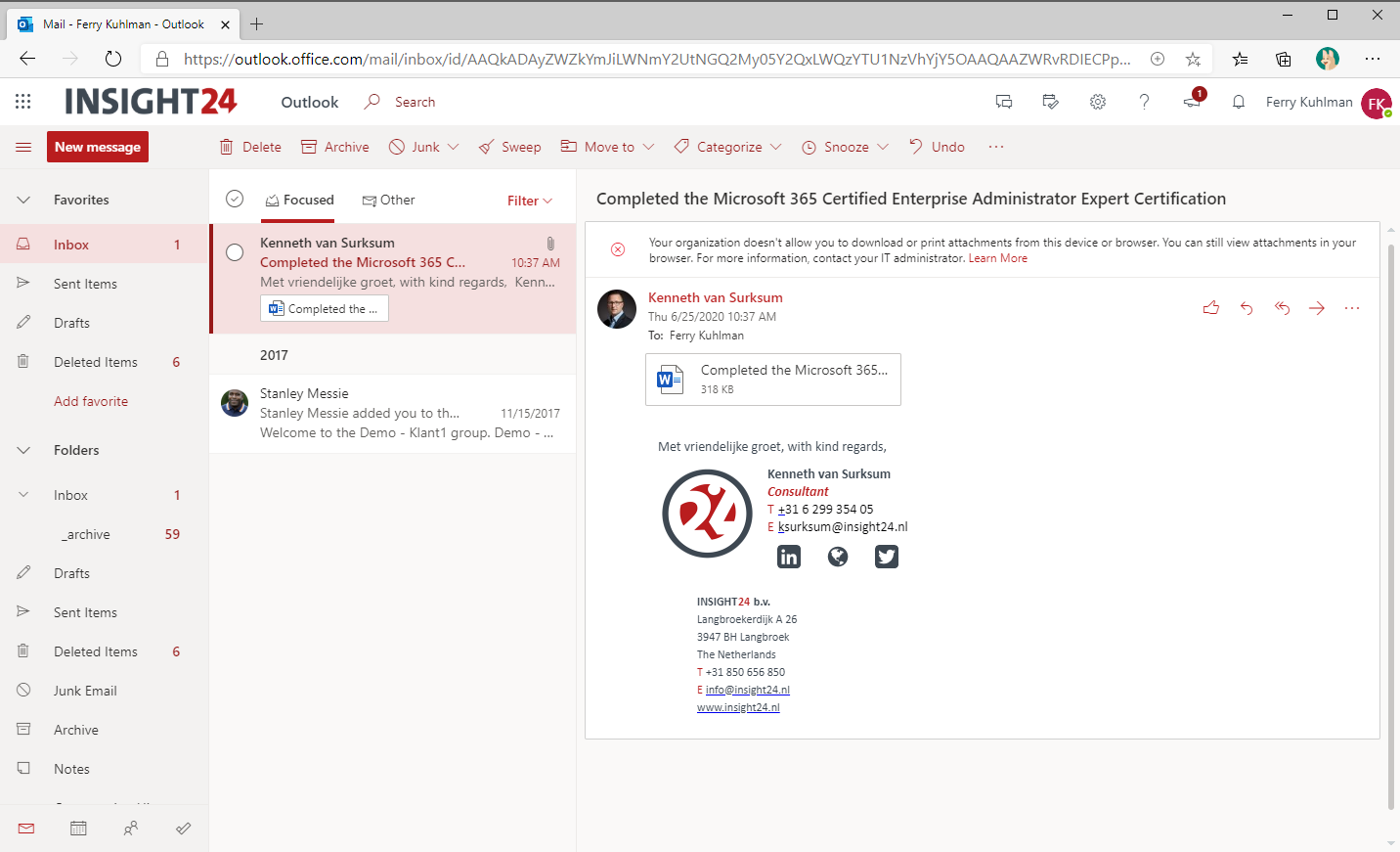
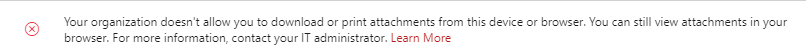
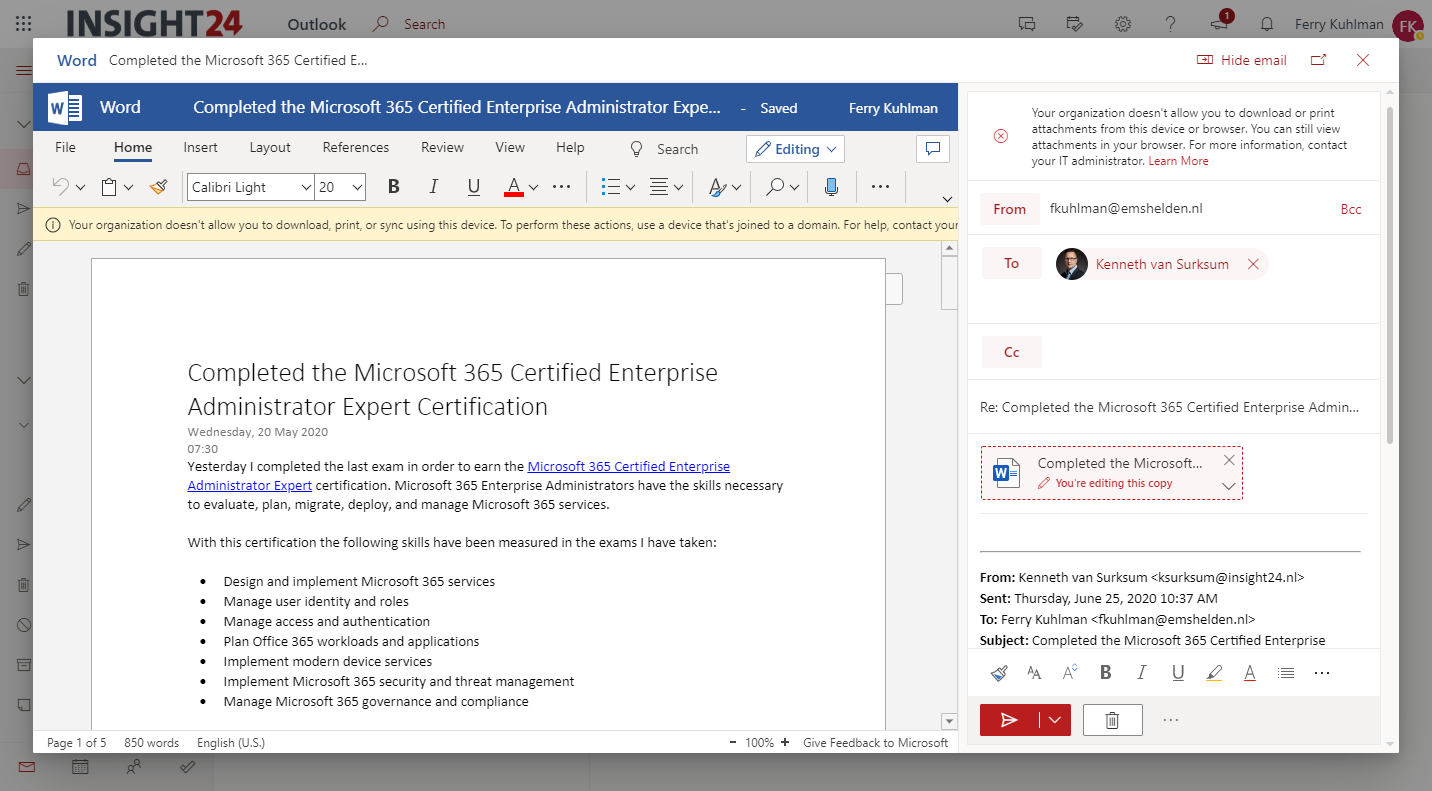
Policy behavior within Outlook Web Access
When the Conditional Access policy is applicable, the user accessing Outlook Web Access experiences the following behavior.
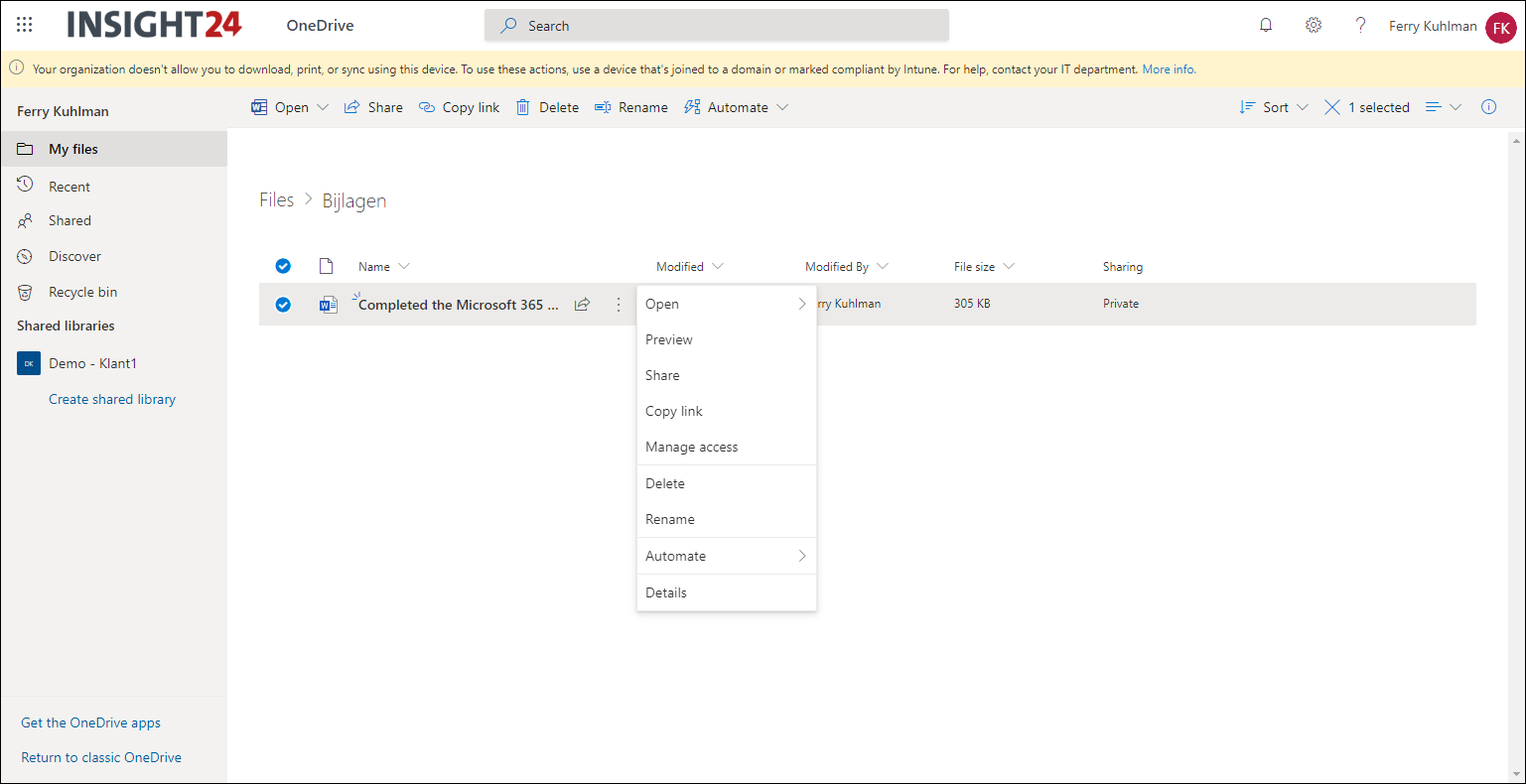
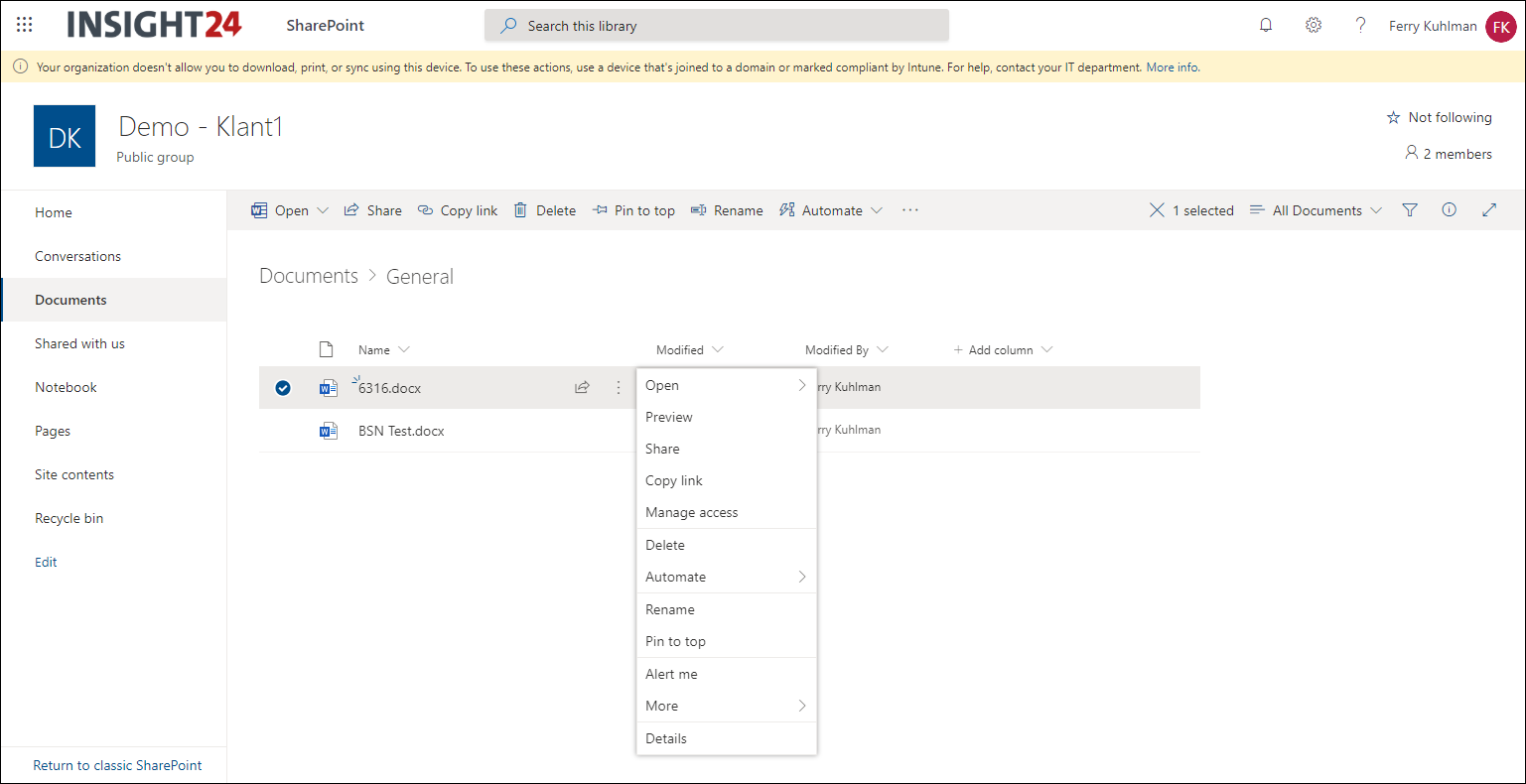
Policy behavior within SharePoint Online and OneDrive
When the Conditional Access policy is applicable, the user accessing SharePoint or OneDrive experiences the following behavior.
Conclusion
Conditional Access App Enforced Restrictions is another piece of the puzzle, allowing you to restrict access to your company data. The options described in this article provide a scenario which should be part of a much broader set of Conditional Access policies which you want to implement in order to protect your company data.
Having some more options to granularly define what can and cannot be done would be helpful, for example blocking the ability to upload files in the policies as well.
In the meantime Microsoft is adding more and more functionality to the sensitivity label functionality, and for which we can use some of that functionality in our Conditional Access scenario’s.
I hope this article provides you with a good idea of what’s possible with Conditional Access App Enforced Restrictions, and the contents of this article will be included in a next version of the Conditional Access Whitepaper. See: “May 2020 update of the Conditional Access Demystified Whitepaper, Workflow cheat sheet, Implementation workflow and Documentation spreadsheet” for the latest available version.
Hi great article 1st of all. But in your last comment about the conditional access rule creation you have not included the Session Use app enforced restrictions component. Is this a typo or ?
Hi Ilias,
Thank you for visiting my blog. You were right, it was definitely a typo. It should be a session control using App Enforced Restrictions. Thank you for bringing this to my attention, modified it right away.
Regards,
Kenneth
Hi Kenneth,
Just wondering if the Block access from apps on unmanaged devices to EXO and SPO should block opening sharepoint/onedrive files from Office Apps. Because i still can open files on sharepoint on an unmanaged windows or mac device, seems strange.
Also the OWA doesn’t seem to block the download option. Policy’s are exactly the same as described above and it’s a test environment so no other CA policies are applied for now.
Hi Tjal,
I’m pretty sure that you missed a step in the configuration. Did you also modify the settings necessary on the SharePoint side? Please also check in your Azure AD Sign-in logging whether the policy is applied to the login of your account.
Thanks for visiting my blog,
Regards,
Kenneth
Hi Kenneth,
Fantastic article and it helped me to resolve my issue.
I have one question, i want to allow user to download the attachment using WEB who is on complaint and Azure AD joined device but dont want to allow him to download from non compliant or Azure AD join device.
do you think it is possible?
Regards
Jag