In my blog article series on Conditional Access Demystied I mentioned that Conditional Access can be used to route sessions toward Microsoft Cloud App Security (MCAS). In this article I will go into more detail on what MCAS is, and how to setup Conditional Access App Control.
Disclaimer: This article discusses the full option MCAS product, there are some other flavors providing partial functionality like Office 365 Cloud App Security and Cloud App Discovery (CAD). For information about licensing, see the Microsoft Cloud App Security licensing datasheet.
What is Microsoft Cloud App Security (MCAS)?
MCAS is Microsoft’s implementation of a Cloud App Security Broker (CASB). So what’s a CASB then you might ask yourself – WikiPedia states the following:
“A cloud access security broker (CASB) (sometimes pronounced cas-bee) is on-premises or cloud based software that sits between cloud service users and cloud applications, and monitors all activity and enforces security policies. A CASB can offer a variety of services, including but not limited to monitoring user activity, warning administrators about potentially hazardous actions, enforcing security policy compliance, and automatically preventing malware.”
Microsoft’s CASB implementation MCAS provides the following functionality:
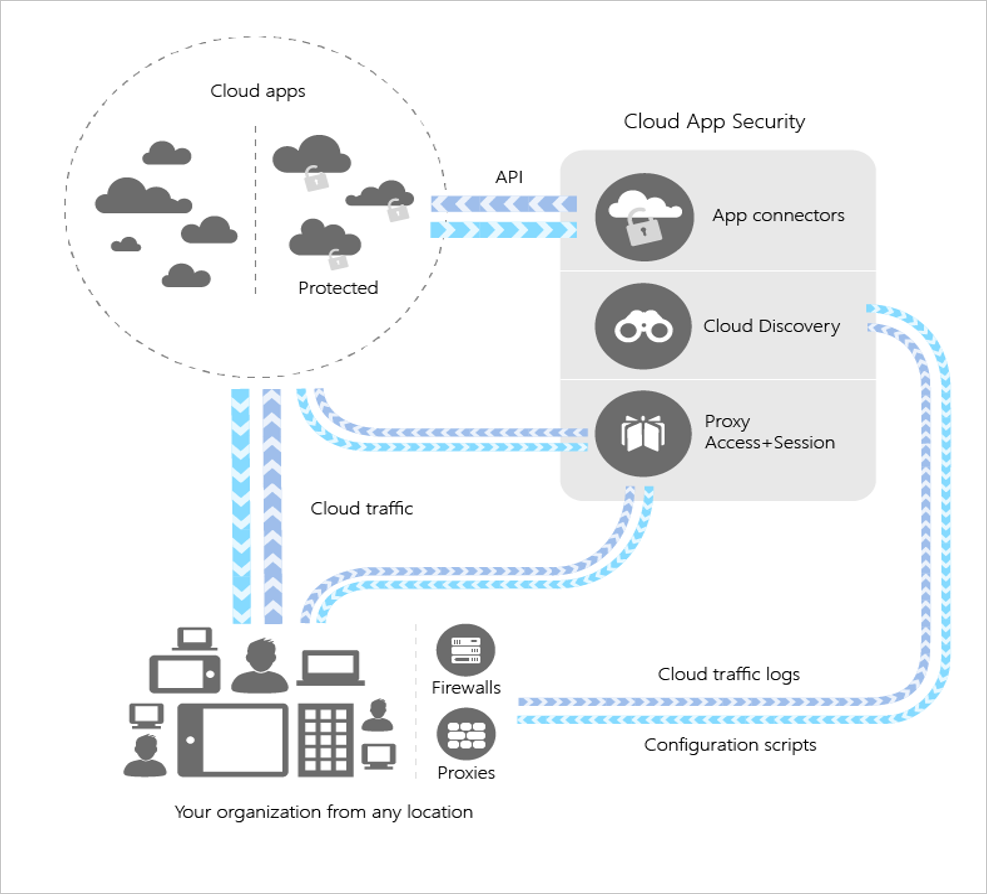
Log Collection also known as Cloud Discovery
By either manual uploading firewall logs (click here to see which FW logs are supported) or setting up an automatic way of doing so, the logfiles are analyzed giving insights in the data concerning cloud applications being accessed from behind the firewall. The main usecase is to gain insights in the so called “Shadow IT” usage, meaning IT services being used within your network out of sight of you (the IT Department).
If you are using Microsoft Defender Advanced Threat Protection (MDATP), you can also enable the connection from MDATP to MCAS allowing for information coming from MDATP to allow machine based investigation, even when machines aren’t on the corporate network and their network traffic doesn’t go through your corporate firewall.
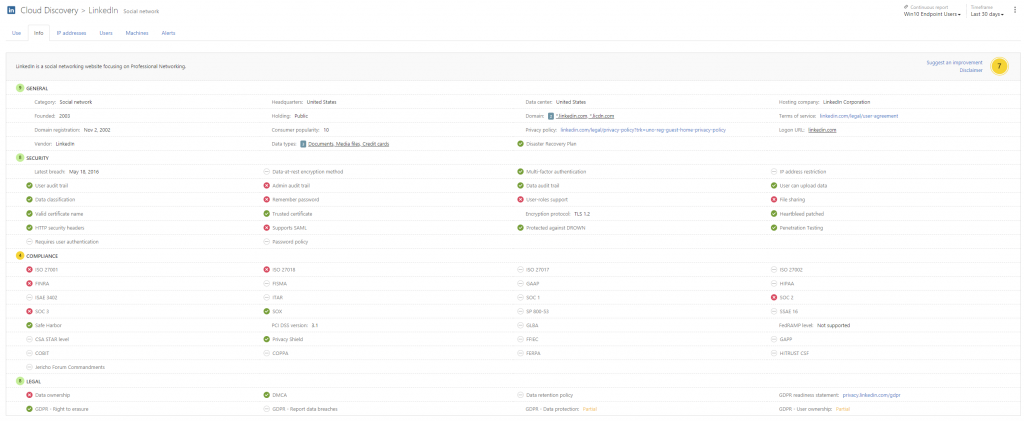
For most applications being discovered, Microsoft provides additional information about Legal, Security and Compliance and based on that calculates a so called Risk Score between 0 and 10. Below is an example of LinkedIn, which has a risk score of 7.
API Connectors also known as App Connectors
By using API Connectors, the information being gathered by MCAS can be extended towards the application services which support this kind of API connection. It’s almost obvious that most Microsoft’s SaaS based apps are supported in this scenario. On the website the following applications supporting API connections are mentioned:
- Office 365
- Box
- Okta
- Gsuite
- ServiceNow
- SalesForce
- Dropbox
- AWS
- Webex
- Workday
What can be discovered is depending on the functionality being provided by the manufacturer of the App. Check this page for more information about what is supported when using the App connector for each product.
Reverse Proxy also known as Proxy Access + Session
By integrating MCAS into your Conditional Access policies, you can redirect user sessions to Cloud Applications through MCAS. MCAS in this case acts a reverse proxy and gives the MCAS administrator the option to govern that session. It’s important to remark that in order to reverse proxy Cloud Application through MCAS, the App must be accessed via Azure Active Directory (Azure AD). If a cloud application is available by other means, like for example with a user account and password coming from another identity provider than Azure AD. (internal mechanism, twitter, google, facebook and so fort). More about this functionality later in this article.
Integration with other and 3rd party products
MCAS provides several integration with other Microsoft products and products from 3rd party vendors. Some examples are that you can use Microsoft Flow when creating policies (more on that later), or integrate with SIEM products or Data Loss Prevention (DLP) solutions.
It’s also possible to integrate MCAS with so called Cloud Proxy solutions, like Zscaler and iBoss. By doing so you are able to block connections for certain cloud services even if clients are not on the corporate network.
MCAS in the Gartner Magic Quadrant for CASB
While writing this article, I noticed some tweets mentioning that research firm Gartner has placed Microsoft in the leader quadrant for CASB solutions, while the report is for paying users only – https://www.gartner.com/en/documents/3892270/magic-quadrant-for-cloud-access-security-brokers. I expect that Microsoft or maybe another mentioned company might make the report available free for download in the near future. If so I will update this article with a link to the report.
What are the use cases voor Conditional Access App Control
The main goal of what we want to accomplish by implementing security products is to keep your users safe and make sure that company data confirms to the Confidentiality, Integrity, and Availability (CIA) triad.
Microsoft has made available a downloadable whitepaper detailing 20 use cases for using a Cloud App Security Broker, which can be downloaded here.
The use cases mentioned are:
- Discover all cloud apps and services used in your organization
- Assess the risk and compliance of your cloud apps
- Goven discovered cloud apps and explore enterprise-ready alternatives
- Enable continuous monitoring to automatically detect new and risky cloud apps
- Detect when data is being exfiltrated from your corporate apps
- Discovery Oauth apps that have access to your environment
- Gain visibility into corporate data stored in the cloud
- Enforce DLP and compliance policies for sensitive data stored in your cloud apps
- Ensure safe collaboration and data sharing practises in the cloud
- Protect your data when it’s downloaded to unmanaged devices
- Enfore adaptive session controls to manage user actions in real-time
- Record an audit trail for all user activities across hybrid environments
- Identify compromised user accounts
- Detect threats from users inside your organization
- Detect threats from privlileged accounts
- Identify and revoke access to risky OAuth apps
- Detect and remediate malware in your cloud apps
- Audit and configuration of your IaaS environments
- Monitor user activities to protect against threats in your IaaS environments.
- Capture user activities within custom cloud on-premis apps
So, how do you configure Conditional Access App Control?
In order to be able to use Conditional Access App Control you must meet the following license requirements:
- Azure Active Directory Premium P1 or higher
- Microsoft Cloud App Security
- Apps must be configured with single sign-on in Azure AD
- Apps must use SAML or Open ID Connect 2.0 protocols
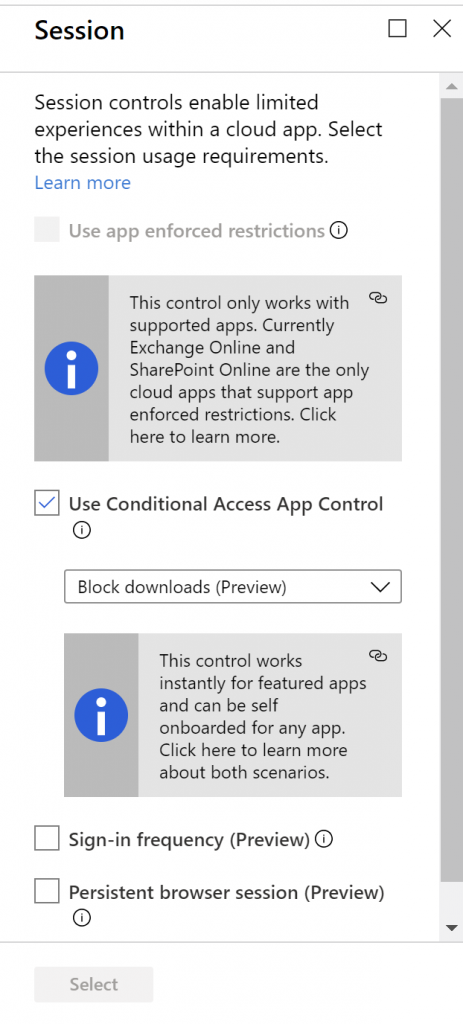
With Conditional Access App Control you can redirect the user’s session to the Cloud App through MCAS. You can start doing this by creating a Conditional Access policy which uses the “Use Conditional Access App Control” session control.
There are featured apps, and apps which must be onboarded first before you can use them with MCAS. Featured apps are:
AWS, Azure DevOps (Visual Studio Team Services),Azure portal (preview), Box, Concur, CornerStone on Demand, DocuSign, Dropbox, Dynamics 365 CRM (preview), Egnyte, Exchange Online, G Suite, GitHub, HighQ, JIRA/Confluence, OneDrive for Business, LinkedIn Learning, Power BI, Salesforce, ServiceNow, SharePoint Online, Slack, Tableau, Microsoft Teams (preview), Workday, Workiva, Workplace by Facebook, Yammer (preview)
Example
In this simple example we are going to configure the following scenario: “We want access to Microsoft teams via the webbrowser from unmanaged Azure AD joined devices to be sent to MCAS so that we can monitoring those sessions and apply policies to them. For this example we are going to Block Downloads from within the session”
Create Conditional Access Policy
- Go to the Azure AD administration portal via: https://aad.portal.azure.com
- Select Azure Active Directory and select Conditional Access
- Click on +New policy to create a new Conditional Access policy
- Provide a name for the new policy, for example “I24 – Route Cloud Services through MCAS”
- Under Users and Group define for which users you want to make the policy applicable. At first it’s advised to do this to a small subset of users. Make also sure to exclude your break glass accounts in order to make sure that no Conditional Access policy hits these account in case something is wrong.
- Under Cloud apps or actions , click on Select apps and select Microsoft Teams
- Under Conditions, select Client Apps (Preview) and select Browser.
- Under Conditions, select Device State (Preview) and under the tab Exclude select “Device marked as compliant”
- Under Access controls, Session select “Use Conditional Access App Control” and select “Block Downloads”
- Save the Conditional Access Policy
Behaviour
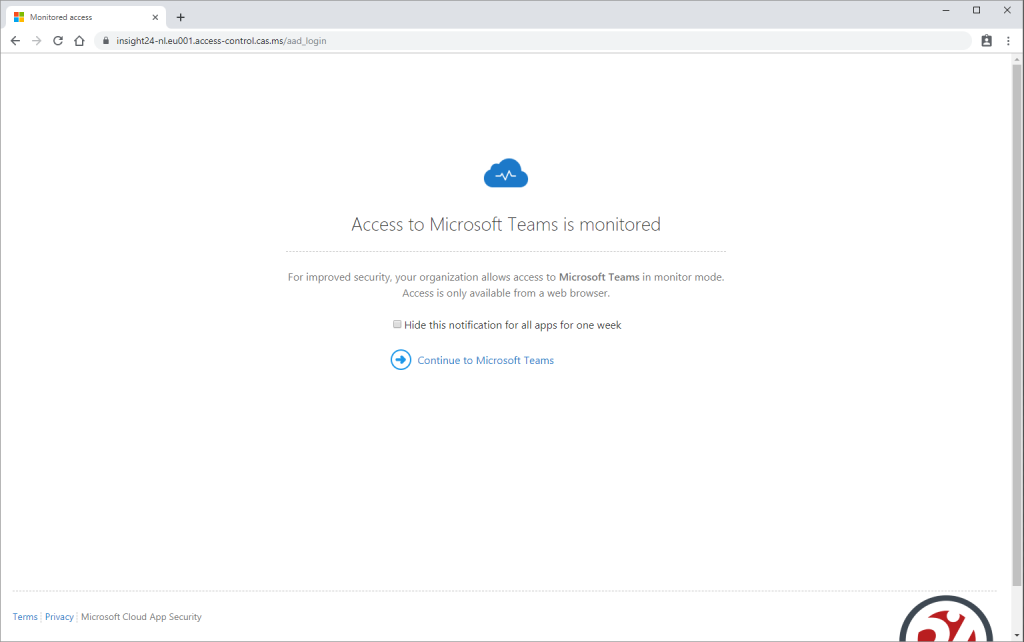
If a user to whom the CA policy is applicable goes to https://teams.microsoft.com on an unmanaged device (or not compliant device), the session is redirected to MCAS. This can be seen by the URL being referenced, in my case: https://insight24-nl.eu001.access-control.cas.ms/aad_login
The first page a user sees, is a custom page (company branded) is diplayed telling the user that Access to Microsoft Teams is monitored. The user has the option to suppress this page for one week, but is reminded again after that.
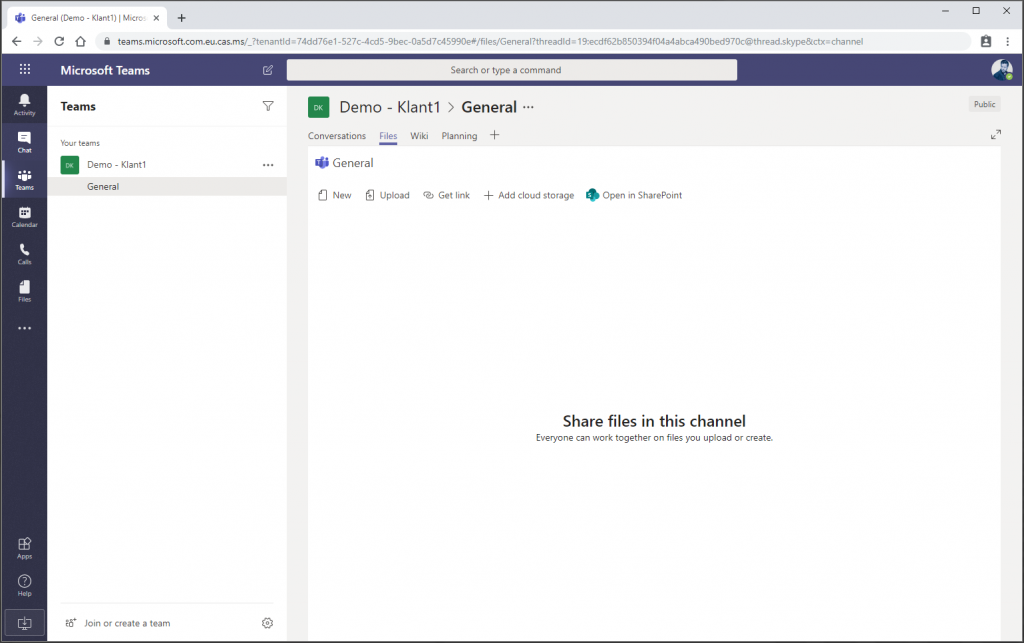
After clicking “Continue to Microsoft Teams” the user is redirected to Microsoft Teams, note though that the URL still points to MCAS
When the user wants to download a file the following screen appears.
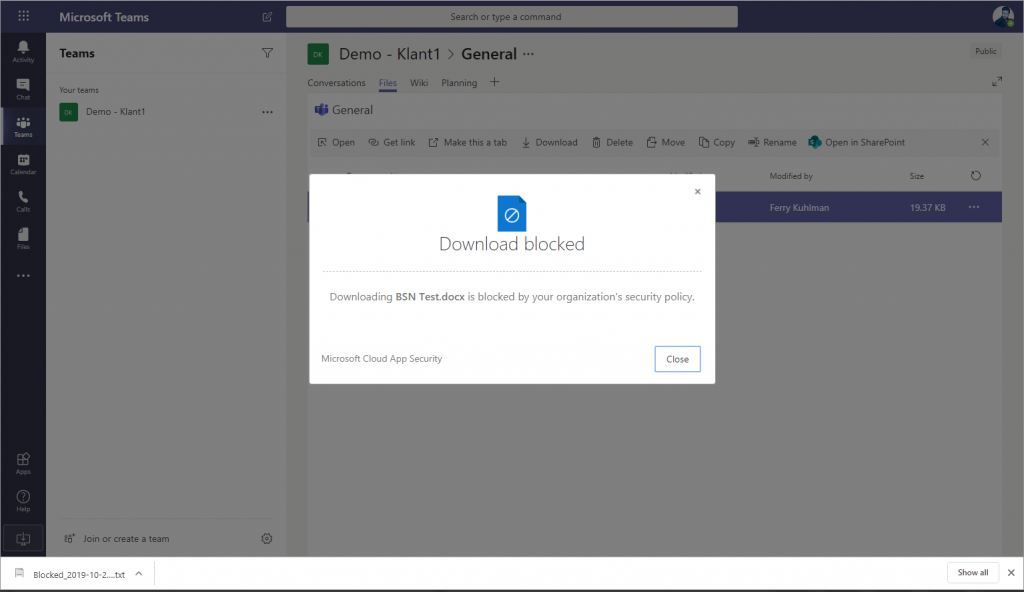
Instead a .txt file is downloaded containing information about the file which was supposed to be downloaded:
The file was blocked since it contained data that is not allowed to be downloaded.
file name: BSN Test.docx
Original file size in bytes: 19373
Original file sha256 checksum: fbfdb872507cd117f6dcc8d208e730979a2158707a36ac05cf06f25b9dfd3aee
Conclusion:
Microsoft Cloud App Security (MCAS) has several usefull security features allowing companies to gain more control about what users are doing with company data. By exending Conditional Access with the Reverse Proxy functionality of MCAS we get even more controls for our Conditional Access policies. While the example above was only a tip of the iceberg about what is possible I hope it gave you an idea of what can be done.
I, myself are also still exploring the numerous features of MCAS, and I hope to describe some more advanced features in a follow up blogposting in the future.
Hi,
Is it possible to implement Conditional Access App Control policy, for example to “block downloads” but for Teams desktop client version?
Hi Karolina,
No I don’t think that will work with an Conditional Access App Control policy, since in this case all the web traffic is reverse proxied through MCAS. We cannot do that with the Teams desktop client version.
Interesting question though, never considered the scenario. If I find something useful I will add that as a comment to this thread.
/Kenneth
You can. It will be an Access policy instead of Session policy.
Session control applies to browser-based apps. To block access from mobile and desktop apps, create an Access policy.
A good write up…
https://janbakker.tech/control-access-from-unmanaged-devices-with-cloud-app-security/
Hi Do you have or can you share any examples of Policies commonly used for Salesforce
Hi Gino,
Unfortunately not, sorry about that!
/Kenneth
Hello, Christopher Brumm wrote blog series about protecting Salesforce with MCAS. Take a look from here:
https://chris-brumm.medium.com/learn-how-to-enable-safer-selling-in-salesforce-with-microsoft-cloud-app-security-part-1-98082b1604d6
Hi Kenneth,
Did you ever find more information on Karolina’s question? I’m curious.
Thanks
You can. It will be an Access policy instead of Session policy.
Session control applies to browser-based apps. To block access from mobile and desktop apps, create an Access policy.
A good write up…
https://janbakker.tech/control-access-from-unmanaged-devices-with-cloud-app-security/
Just to be clear: yes, you can block access TO desktop apps with Cloud App Security. No, you cannot block downloads IN desktop apps with Cloud App Security 😉 That is a heavily requested feature, but I don’t see it happen anytime soon to be honest. All traffic have to be proxied, so unless that desktop app is acting like a browser, the session cannot be controlled (yet).
Would you be able to use this to say block android and iOS devices from accessing an SSO SaaS app like AWS or Mongo Atlas?
Hi Adrian,
Yes, that would be a possible scenario, the device should be MDM managed if you really want to enforce this though – since when using MAM and enforcing Microsoft Defender enrollment, the user can still turn off the VPN which is necessary to enforce blocking access to cloud services.
Could you implement this to enforce an MFA push when elevating permissions, ie Azure PIM
Mark,
I would just use Authentication Context for this.. so define the authentication context in PIM, and create a CA policy using that auth context to enforce (preferably strong) MFA
/Kenneth